AI + Quantum Cybersecurity: The Major Shifting Point Now in 2026
In eight weeks this spring, the cybersecurity arms race changed twice. On March 10, Fortinet shipped FortiOS 8.0, the first major operating system to embed AI governance, agentic-AI visibility, and quantum-safe cryptography into a single security fabric. On April 30, FortiGuard Labs released the 2026 Global Threat Landscape Report and put a hard number on […]
Why “Unpatched” is a Warning Now to Businesses
Does your business run on VMware vSphere? If so, continue reading. vSphere 7 is already past End of General Support. vSphere 8 will follow in October 2027. And on April 7, 2026, Anthropic disclosed an AI model that can autonomously find and weaponize zero-day vulnerabilities at industrial scale. What does this mean for you and […]
The VMware Crossroads in 2026: Rising Costs, Partner Changes, and Smarter Infrastructure Choices

VMware customers are entering a new era of pricing pressure, partner disruption, and strategic uncertainty. Here is what changed in 2026, why it matters, and how businesses are responding with private cloud, hybrid infrastructure, and long-term risk reduction.
Server and PC Hardware Prices Are Rising in 2026: What’s Driving It and What It Means for IT Budgets
Across the next 2–3 quarters (Q1–Q3 2026), many organizations should expect continued upward pressure on server and PC hardware pricing. The biggest near-term drivers are not always CPUs or chassis—pricing is being pushed primarily by memory (DRAM) and flash storage (NAND/SSD), compounded by AI-driven demand and procurement volatility. Executive Summary What’s Actually Getting More Expensive […]
Veeam’s Acquisition of Securiti AI: Why It Matters for Backup, Security, Compliance, and AI at Scale
Enterprises are moving from “backup as an insurance policy” to “backup as a strategic data asset.” That shift is accelerating fast—and Veeam’s acquisition of Securiti AI is one of the clearest market signals yet. In late 2025, Veeam announced and completed its acquisition of Securiti AI for approximately $1.725B, positioning the combined portfolio around what […]
What the November 18 2025 Cloudflare Outage Means for Businesses — Who, What, When, Where, and Why
On 18 November 2025, Cloudflare — a critical piece of internet infrastructure relied upon by millions of websites and services — experienced a widespread outage. For businesses that depend on web-apps, APIs, content delivery networks (CDNs) or DDoS protection platforms, this event is a wake-up call. In this article we break down the who, what, […]
AWS’s October 20, 2025 Outage: A Hard Reset on Single-Cloud Thinking

Why “too big to fail” is too big a risk—and how a private-cloud failover posture derisks your uptime, compliance, and brand equity Executive Summary On October 20, 2025, a major AWS US-EAST-1 incident degraded a wide swath of the internet—disrupting consumer apps, enterprise SaaS, and key public services. Amazon attributed the core fault to DNS […]
Veeam and VMware Cloud Director Integration: Simplifying Backup and Recovery in Multi-Tenant Clouds
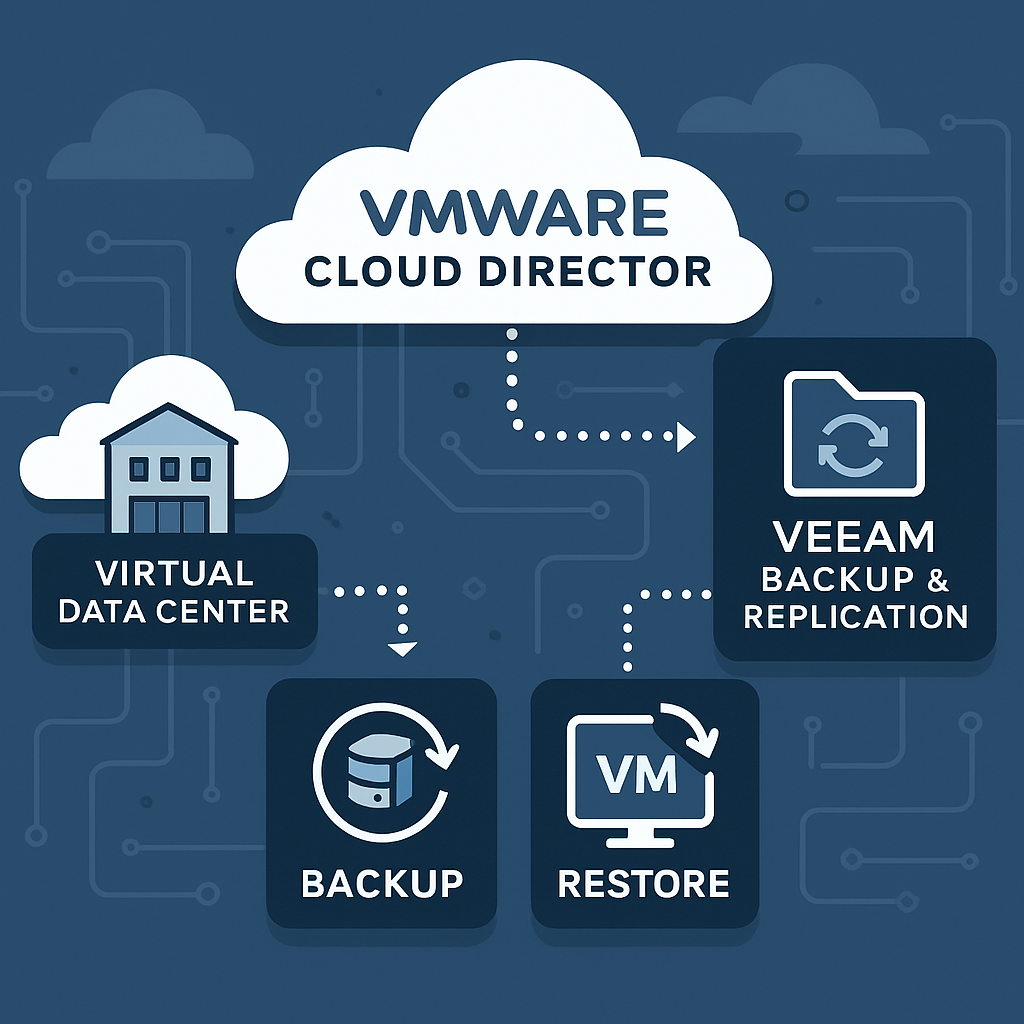
In today’s hybrid-cloud landscape, enterprises are blending on-premises virtualization with hosted services from managed providers. VMware Cloud Director (formerly vCloud Director) enables service providers to deliver secure, multi-tenant virtual data centers (VDCs) to customers, while Veeam Backup & Replication provides proven backup and recovery for VMware workloads.Integrating the two delivers a powerful, service-provider-grade solution for […]
AI-Native Cloud Infrastructure: The Next Frontier for Enterprise IT in 2025
Introduction In 2025, cloud infrastructure evolves beyond mere virtualization and scalability — we’re entering the era of AI-native cloud infrastructure, where artificial intelligence is deeply embedded at every layer of the stack: networking, compute, storage, security, and operations. For organizations architecting resilient and future-proof systems, AI-native clouds aren’t optional — they’re a strategic imperative. In […]
VMware Cloud Foundation 9.0: Redefining Private Cloud — And How IT Vortex Delivers It
VCF 9 is Here By Lou Corriero, VP – Business Development & Cloud Technologies, IT Vortex, LLC Introduction The evolution of private cloud has reached a milestone with VMware Cloud Foundation 9.0 (VCF 9.0). Launched on June 17, 2025, this major release redefines on‑prem infrastructure by converging performance, agility, compliance, and developer self‑service—all under a unified operational […]






















