In eight weeks this spring, the cybersecurity arms race changed twice. On March 10, Fortinet shipped FortiOS 8.0, the first major operating system to embed AI governance, agentic-AI visibility, and quantum-safe cryptography into a single security fabric. On April 30, FortiGuard Labs released the 2026 Global Threat Landscape Report and put a hard number on what attackers have already done with AI: 7,831 confirmed ransomware victims in 2025, a 389% year-over-year increase, with time-to-exploit compressed from days to hours. The “preparing for the future” framing is over. The future arrived.
The Eight-Week Window That Ended the Planning Era
For two years, AI cybersecurity and quantum-safe protection were boardroom conversations about preparing building roadmaps, evaluating vendors, and sequencing migrations against vague three-to-five-year horizons. Two announcements in March and April collapsed that timeline.
The first was Fortinet’s FortiOS 8.0 launch at Fortinet Accelerate 2026 in Las Vegas. It is the operating system underneath the Fortinet Security Fabric the platform that runs on FortiGate firewalls, FortiAnalyzer, and the rest of the Fortinet portfolio and the 8.0 release is structured around three concurrent shifts: AI-driven security, next-generation SASE, and quantum-safe protection. Not a roadmap. A shipping product.
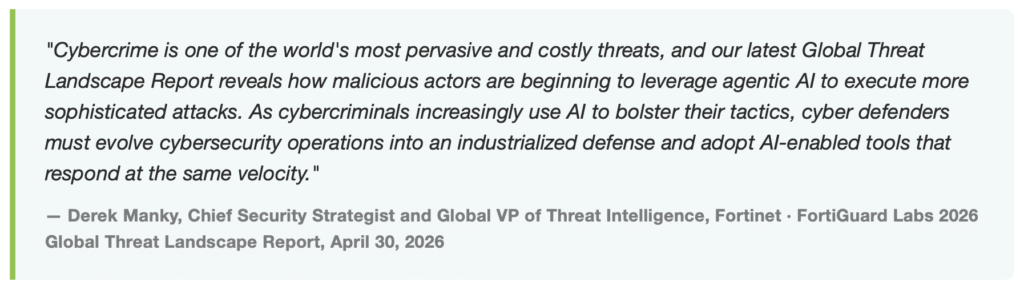
The second was FortiGuard Labs’ 2026 Global Threat Landscape Report, published April 30. It is the empirical case that adversaries are not “exploring” AI. They are operating with it.
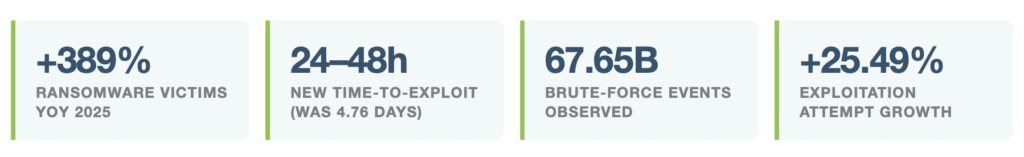
Each of these numbers is from FortiGuard Labs telemetry covering 2025. The headline figure 7,831 confirmed ransomware victims is not an extrapolation. It is the count of victim postings on dark-web leak sites that FortiRecon mapped to specific compromised organizations. The +389% year-over-year change is not a trend line projecting upward. It is what already happened while most security teams were still arguing about whether GenAI in the SOC was worth the procurement cycle.
What “AI Cybersecurity” Actually Means in 2026
The phrase “AI cybersecurity” has been overused into near-meaninglessness. Three distinct things hide under that umbrella and IT leaders evaluating their posture need to be precise about which one they are buying because the gaps are not the same.
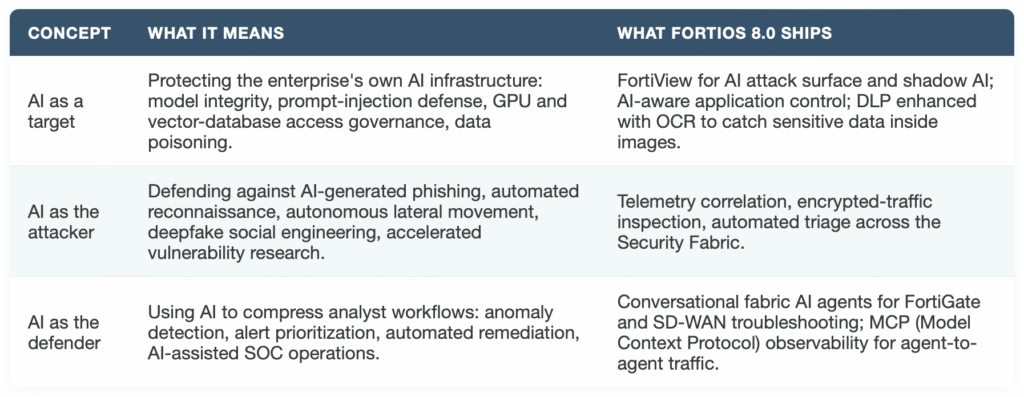
The new entry on this list, and the one most IT leaders have not absorbed yet, is the middle row of column three: MCP observability. The Model Context Protocol is how autonomous AI agents pass context to other agents and to applications. Without visibility into MCP traffic, agentic AI runs outside the controls a CISO can see sanctioned or not. FortiOS 8.0 is the first major firewall OS to provide telemetry on agent-to-agent (A2A) and MCP interactions. That is a quietly large shift. It moves agentic AI from a category that bypasses governance to one that can be governed.
Why the Time-to-Exploit Number is the One CFOs Need to See
If a finance executive at a $500M company can absorb only one statistic from the FortiGuard report, it is this: time-to-exploit compressed from 4.76 days to 24–48 hours. Time-to-exploit (TTE) measures the interval between a vulnerability being disclosed and its exploitation appearing in live attack telemetry. Five days was a thin window. One to two days is operationally a different game.
Patching cadences, change windows, and vulnerability management programs were designed around days-to-weeks. With TTE collapsed to 24–48 hours, two things stop working at the same time: the assumption that internal IT teams can read CVE advisories on Tuesday and patch by Friday, and the assumption that endpoint detection alone will catch what slips through. The vulnerability disclosure cycle has been industrialized by adversaries using AI to accelerate exploit development. Defenders need an industrialized response in return which is exactly the framing Fortinet’s threat-intelligence team chose for the 2026 report.
The Quantum-Safe Layer is Not a 2030 Problem Anymore
Quantum computing’s threat to modern encryption has been a slow-burning concern for years. The dominant threat model is called “harvest now, decrypt later”: adversaries capture encrypted traffic, VPN sessions, and stored archives today, and decrypt them when quantum capabilities mature. Sensitive data with multi-year retention requirements patient records, legal discovery, financial trade detail, intellectual property, and government archives are already at risk under this model, regardless of when the first cryptographically relevant quantum computer comes online.
FortiOS 8.0 introduces production support for FIPS 204/205 hybrid key exchange, combining classical encryption with quantum-resistant algorithms. It extends post-quantum protection to SSL deep inspection, agentless VPN connectivity, and management access paths. ML-DSA certificates are supported for authentication and key establishment. These are not laboratory features. They are configurable on shipping FortiGate appliances.
For most enterprises, the quantum migration is not a firewall firmware update. It is a multi-year inventory and replacement program covering thousands of certificates, legacy VPN concentrators, embedded systems, third-party APIs, and identity platforms whose cryptographic dependencies were never documented. The realistic move now is not “rip and replace.” It is crypto agility building the operational ability to swap algorithms as standards finalize, starting with the highest-leverage paths: management plane, encrypted traffic inspection, and remote access.
What Changes Inside the Security Fabric
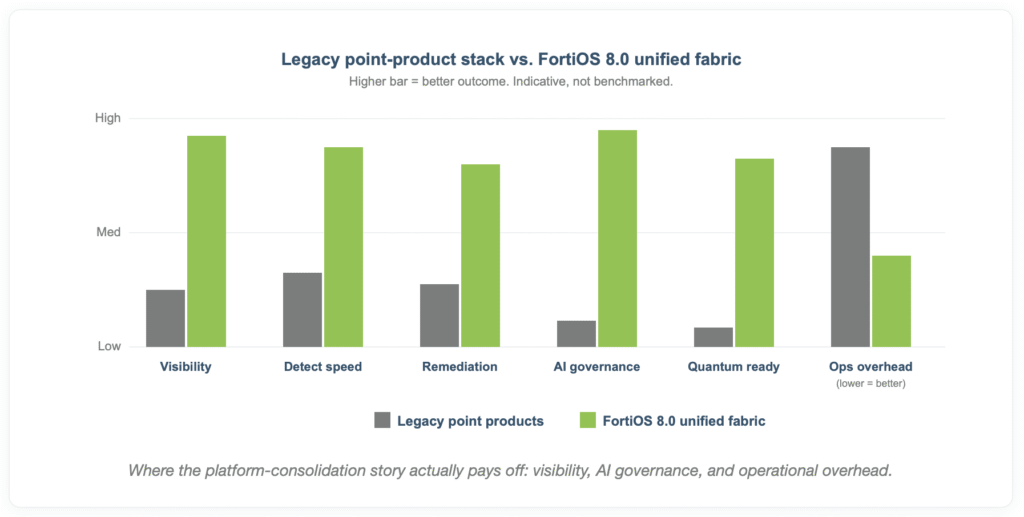
The thing FortiOS 8.0 does that point products cannot is collapse the seams. A typical mid-market enterprise runs 20–40 disconnected security tools. AI-driven attacks exploit the seams between those tools, the gaps where telemetry from a SIEM doesn’t reach the firewall, where the EDR alert never gets correlated with the identity event, where the SASE policy contradicts the on-prem segmentation. The Security Fabric is structurally a counter to that problem: shared intelligence, consistent policy, and one operating system layer across firewall, SASE, SD-WAN, and SOC.
The “Harvest Now, Decrypt Later” Timeline Visualized
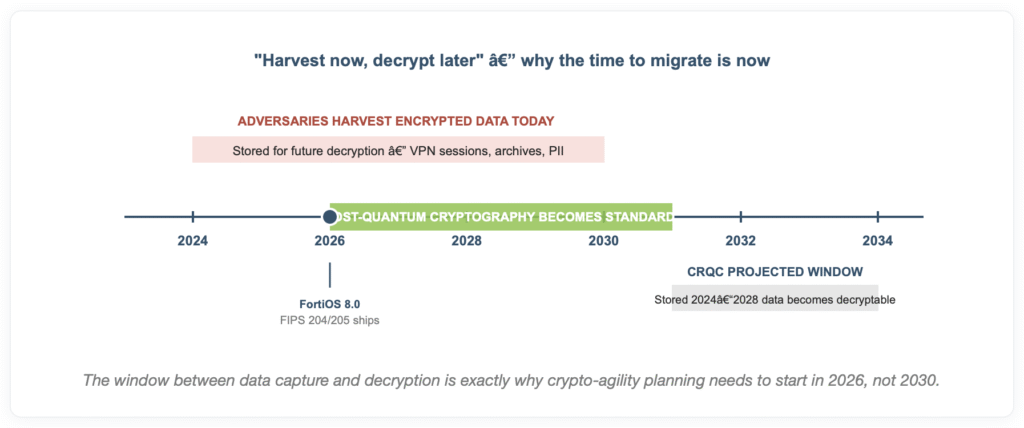
A useful mental shortcut: anything you protect today that needs to remain confidential into the early 2030s should already be on a post-quantum migration plan. For most regulated industries, that’s most of the data on the network.
The Platform Consolidation Case Measured in Lost Tools, Not Added Ones
The strategic argument behind a Security Fabric isn’t “buy more from one vendor.” It is “operate fewer products.” The cybersecurity industry consensus, captured in every analyst conversation of the last two years, is that the average enterprise will spend the next 36 months shrinking its security tool inventory not expanding it. Tool sprawl, alert fatigue, license overlap, and integration overhead now cost more than the threats some of those tools were procured to defend against.
The 67.12% of dark-web “database” activity that FortiRecon classifies as stealer logs is a useful proxy for what attackers prioritize: not sophisticated zero-days, but compromised endpoints whose telemetry never lit up across disconnected security tools. Stealer logs are a tool-sprawl outcome made profitable. Consolidating to a single fabric isn’t about vendor lock-in. It’s about closing the gaps where stealer logs are being generated in the first place.
Who Else is Moving the Ecosystem Signal
One way to read whether a technology shift has actually arrived is to look at which organizations are repositioning around it. The signal across the FortiOS 8.0 timeframe is strong.
On the AI infrastructure side, NVIDIA has become the dominant compute provider for both enterprise AI workloads and quantum-classical hybrid simulation through its CUDA-Q platform. The same GPU clusters that train internal LLMs are now also the high-value attack surface that FortiOS 8.0’s AI-aware controls are designed to govern. Microsoft, AWS, and Google have all aligned their security platforms around AI-assisted SOC operations and post-quantum readiness, and Broadcom Fortinet’s hardware silicon partner and now the owner of VMware is shipping post-quantum capabilities into the underlying network and virtualization layers.
The U.S. National Institute of Standards and Technology (NIST) finalized the first wave of post-quantum cryptographic standards in 2024, and the federal government has set 2030-2035 as the deadline for transitioning agency systems off vulnerable algorithms. Major cloud providers are committing to PQC-capable services on a similar timeline. The vendors are not waiting on customers, and customers who wait on vendors will find the migration cost concentrated into the last 18 months of the window when professional services capacity is gone.
For organizations running Fortinet, the load-bearing point is that the work to integrate FortiOS 8.0’s AI and quantum-safe capabilities is happening on the vendor’s release cadence, not the customer’s planning cadence. The capabilities are showing up in firmware. The decision is whether to operate them or to skip versions and lose the benefit.
When — Not If — This Hits Your Organization
The translation from threat-report numbers to specific business consequences runs through three predictable paths:
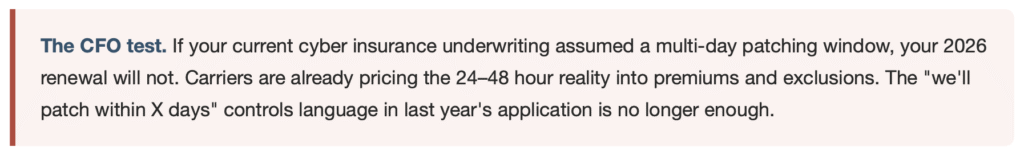
- Cyber insurance renewal becomes harder. Underwriters are already using time-to-exploit compression and ransomware victim counts in the 2026 renewal cycle. Organizations without documented AI-aware controls or roadmap evidence for post-quantum migration are seeing premium increases, sub-limit reductions, and tighter exclusionary language. Roughly one in five denied claims in 2024–2025 tied back to unsupported software or weak controls language.
- Board-level AI risk questions arrive without warning. Directors who read the same Wall Street Journal article about agentic AI now expect a coherent answer from IT about “what do we have in place.” Not having one is a credibility event, not a technical event.
- A shadow-AI incident lands first. Most enterprises will discover their AI exposure not from a sophisticated targeted attack but from a marketing manager pasting a customer list into a public LLM, or an engineer using an unsanctioned coding assistant against a production codebase. FortiView for AI shadow AI was built specifically for this incident shape.
The IT Vortex Safe-Path
The honest reading of the FortiOS 8.0 announcement is that it’s a strong product release that closes real gaps in the AI-attack and post-quantum threat models. The honest reading of the FortiGuard 2026 report is that those gaps are already being exploited at scale. The question for most IT executives is not “should we adopt this stack.” It is “do we have the people, time, and budget to run it ourselves.”
For most mid-market and enterprise organizations, the answer is no and that is where IT Vortex’s positioning is sharpest. We are a Fortinet partner running the Security Fabric in production for clients today. The capabilities in FortiOS 8.0 are not aspirational on our managed platform. They are our customers’ next firmware cycle.
Security as a Service (SECaaS) — managed Fortinet, fully operated
We deploy and operate FortiGate, FortiAnalyzer, FortiManager, and the broader Security Fabric for clients as a managed service. That means 24/7 monitoring against FortiGuard threat intelligence, policy administration, change control, incident response, and quarterly posture reviews all delivered against an SLA. Customers don’t staff an in-house SOC to get SOC outcomes. The new AI-aware controls and quantum-safe configurations from FortiOS 8.0 get integrated into the managed service automatically, in the regular firmware progression. There is no separate procurement for the AI part or the quantum part.
Cloud Hosting (IaaS) — secure-by-default workload platform
Our VMware-powered private cloud is segmented, monitored, and Fortinet-protected at the perimeter and east-west. Workloads that move from on-prem to IT Vortex’s cloud inherit a security posture that the customer would otherwise be responsible for designing, hardening, and maintaining. That posture includes encrypted traffic inspection, segmentation policy, and the same telemetry pipeline that feeds the SECaaS team.
Disaster Recovery (DRaaS) — the recovery side of the ransomware equation
Ransomware events are not just an attack-surface problem. They are a recovery-time problem. Our DRaaS platform provides push-button failover, immutable backup targets, continuous VM replication, and tested recovery playbooks. When the 24–48 hour time-to-exploit number translates into a real incident, the difference between a four-hour recovery and a four-week recovery is whether the DR was managed or improvised.
About IT Vortex. IT Vortex is a Fortinet partner and Premier Broadcom VCSP Partner headquartered at 237 W Midland Ave, Paramus, NJ. We provide managed cloud, security, and recovery services: Cloud Hosting (IaaS), Desktop as a Service (DaaS), Disaster Recovery (DRaaS), Backup as a Service (BaaS), and Security as a Service (SECaaS) to mid-market and enterprise organizations across the Northeast and nationally. 1 (844) 704-0684 · [email protected] · theitvortex.com
Sources
- Fortinet, “Fortinet Introduces FortiOS 8.0 to Expand Secure Networking with Secure AI Controls, Fabric-based AI Agents, Flexible SASE, and Simplified SD-WAN,” March 10, 2026.
- Fortinet, “Fortinet 2026 Global Threat Landscape Report Reveals a Surge in AI-Enabled Cybercrime, Contributing to a 389% Increase in Ransomware Victims Year-over-Year,” April 30, 2026.
- Fortinet Blog, “FortiOS 8.0: Redefining Secure Networking in the AI and Quantum Era,” April 6, 2026.
- Futurum Group, “Fortinet FortiOS 8.0 Pushes Secure Networking To AI Governance,” March 16, 2026.






















