Why “too big to fail” is too big a risk—and how a private-cloud failover posture derisks your uptime, compliance, and brand equity
Executive Summary
On October 20, 2025, a major AWS US-EAST-1 incident degraded a wide swath of the internet—disrupting consumer apps, enterprise SaaS, and key public services. Amazon attributed the core fault to DNS resolution issues impacting DynamoDB regional endpoints, which cascaded across load balancers and dependent services. The outage began in the early hours of the U.S. morning and took hours to fully stabilize, impacting household names from Snapchat, Fortnite, Roblox, Alexa, Ring, Coinbase, Robinhood and more, with knock-on effects across commerce, fintech, media, higher education, and government digital services. (Amazon News)
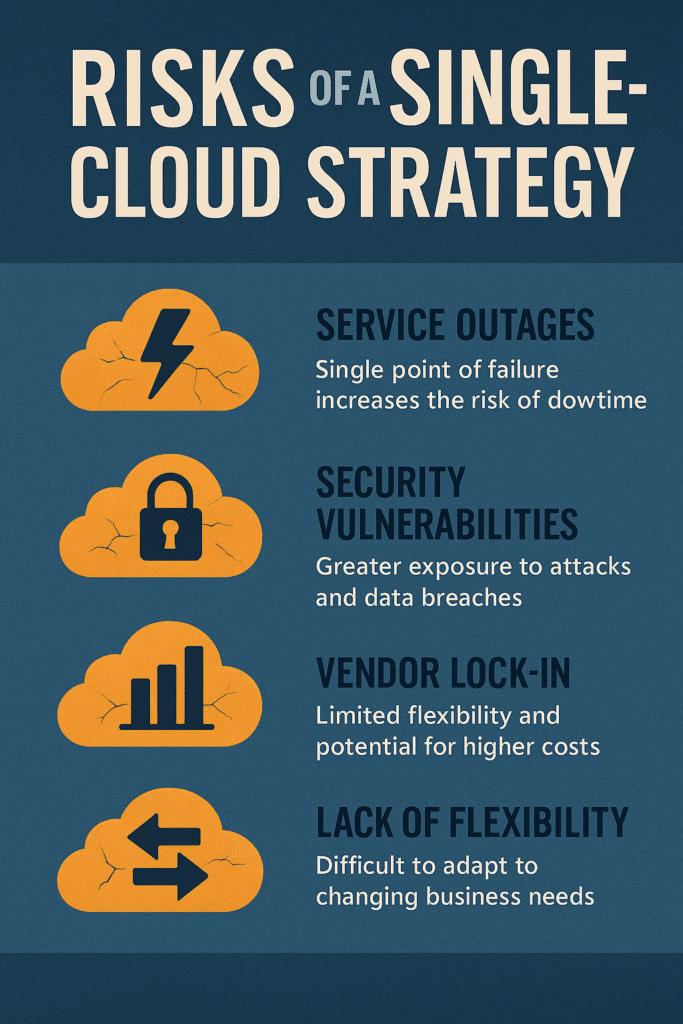
Beyond the headlines, the strategic signal is clear: Single-cloud concentration is a material operational risk. When one hyperscaler sneezes, the internet catches a cold. If this had been a hostile cyber event instead of a technical fault, the impact could have been existential for businesses without an independent recovery plane. A private-cloud failover capability—paired with multi-region/multi-provider design—turns a day-ending outage into a controlled, auditable failover event that protects SLAs, revenue, and brand trust.
IT Vortex’s VMware-powered private cloud provides the alternate landing zone and predictable runbook to keep you transacting when the public cloud gets turbulent.
The Signal Behind the Noise: What Actually Happened
On October 20, 2025, AWS US-EAST-1 (Northern Virginia) experienced increased error rates and latencies across multiple services. Within an hour, AWS engineers isolated the likely root cause: DNS resolution failures for the DynamoDB API endpoint in the region. That, in turn, knocked on to load balancers and dependent platform services, forcing widespread timeouts and failures for applications pinned to US-EAST-1. Amazon says mitigation began around 2:24 AM PDT, with continued stabilization during the day and a full return to normal operations declared by evening. (Amazon News)
Third-party observability teams (e.g., ThousandEyes) corroborated the US-EAST-1 blast radius, noting outages across major consumer and enterprise platforms tied to AWS regional endpoints. Some reports additionally noted DNS and EC2 internal network health monitor interactions that amplified the incident’s footprint. (ThousandEyes)
Key timeline highlights (Oct 20, 2025; U.S. times):
- ~12:11 AM PDT – AWS observes increased error rates and latencies in US-EAST-1.
- ~1:26 AM PDT – Elevated errors to the DynamoDB endpoint acknowledged.
- ~2:24 AM PDT – Mitigations applied; service recovery begins, residual issues persist.
- Later in the day – AWS and major apps continue staged recovery; Amazon announces normal operations restored by evening. (The Register)
Who Was Affected—and Why It Mattered
The outage impacted a broad portfolio of high-traffic, high-dependency services, illustrating how platform concentration in a single region/provider becomes a systemic fragility:
- Consumer & Social: Snapchat, Reddit, Roblox
- Gaming: Fortnite, Epic Games Store, Pokémon Go
- Voice/Smart Home & Video: Alexa, Ring, Prime Video
- Fintech & Crypto: Coinbase, Robinhood, Venmo
- SaaS & Productivity: Airtable, Zapier, Canva, Slack (via dependencies)
- Public Sector & Education: HMRC (UK), university systems (e.g., Canvas, Zoom access)
- Commerce: Amazon.com services themselves saw impairment windows
Reports also cited Lloyds and Halifax (UK banking), and Zoom access degradation via platform dependencies. (The Guardian)
At peak, media estimated millions of users experienced disruption, with elevated complaint volumes on outage trackers for hours. Markets and equity analysts again flagged US-EAST-1 as a single failure domain with outsized systemic blast radius—echoing earlier years’ outage lessons. (Reuters)
The Hidden Physics of Hyperscale: Why One Region Can Break Your Day
Many organizations build “HA” architectures that are region-local (multi-AZ), but not region-agnostic. When a regional control plane or a shared underpinning service (like DNS to a managed data plane) falters, multi-AZ resilience isn’t enough. Dependencies on regional endpoints, identity gateways, or centralized telemetry can create invisible choke points. Yesterday was a textbook example: a DNS issue impacting a foundational data service (DynamoDB) propagated through load balancers and dependent services, kneecapping apps that assumed regional isolation was sufficient. (Reuters)
Translation: Multi-AZ ≠ Multi-Region. And Multi-Region ≠ Multi-Provider.
Resilience is a spectrum, and yesterday’s event exposed where many architectures sit on that spectrum.
If This Had Been a Cyber Event—Not a Technical Fault
AWS reports this was not a malicious attack but a technical incident rooted in DNS and service health mechanisms. Still, the operational blast radius offers a sobering proxy for what a targeted cyber event could achieve:
- Coordinated DNS poisoning or control-plane compromise could create similar or worse symptoms, persist longer, and impact data integrity.
- Credentialed abuse or supply-chain exploits (e.g., dependency on cloud-native management services) could outmaneuver typical runbooks.
- Regulated industries would face heightened reporting, forensics, and customer communication obligations with legal/compliance exposure.
When your continuity posture is single-provider, you’re effectively betting that the same provider will not experience a multi-vector event that hits both the production stack and the recovery tooling. That’s an unhedged risk.
The Bigger Picture: Concentration Risk in a Three-Horse Cloud Race
Analysts and industry commentators immediately framed the outage as another reminder that too much of the internet is concentrated behind a handful of clouds. When AWS, Microsoft Azure, or Google Cloud stumbles, the collateral impact is macro-scale. Recent coverage underscored the societal and economic risk of this concentration and questioned whether hyperscalers should be regulated like critical infrastructure. (The Guardian)
From a board-level perspective, this isn’t merely an IT story; it’s a business continuity, reputational risk, and shareholder value story. OpEx volatility from downtime, contractual penalties, lost transactions, and customer churn can outstrip any savings from centralized hosting. Yesterday’s event simply priced that risk in—again.
Root Cause at a Glance (Non-Jargon)
- What failed? DNS resolution for DynamoDB regional endpoints in US-EAST-1—a foundational managed database service many apps rely on.
- What did that break? Load balancers and dependent AWS services experienced health check anomalies and request failures; apps relying on those services timed out or errored.
- Why was the impact so big? Many apps centralize critical control-plane and data-plane dependencies in US-EAST-1 for latency, history, or convenience—making it a single failure domain for operational reality.
- How long did it last? Mitigation began pre-dawn U.S. time; full normalization was declared later in the day, though recovery varied by service. (Reuters)
Lessons Learned: Design for Failure, Not for Hope
1) Your RPO/RTO are only as good as your independent recovery plane
Backups inside the same provider are not independence. If identity, DNS, and control planes are impacted, can you still authenticate, decrypt, route, and run? A private-cloud failover with pre-staged runbooks and network reachability gives you an orthogonal path to continuity.
2) Region escape hatches are table stakes
Even “serverless” and managed-service heavy workloads need a region-escape blueprint: replicated state (databases, object storage), dual-homed service discovery, and feature flags to reroute traffic on command. Yesterday underscored how regional DNS/data service coupling can disable even “stateless” front-ends.
3) Provider diversity limits correlated failure modes
A design that can move or restart critical business capabilities on a second platform—public or private—reduces the chance that a single provider’s cross-cutting incident becomes your outage too.
4) Operational rehearsals beat architecture diagrams
Failovers fail when they’re theoretical. Quarterly game-days that test identity, DNS, routing, app state, and observability across providers convert architecture into muscle memory.
What Companies Should Do Now (Actionable Controls)
- Map provider-coupled dependencies
Catalog every workload’s DNS, identity, data, and queuing dependencies. Flag regional hard-pins (e.g., US-EAST-1) and managed data services (e.g., DynamoDB) without cross-region failover. - Stand up an independent recovery plane
Deploy an alternative run environment on IT Vortex’s VMware-powered private cloud. Pre-stage images, configuration, secrets handling, and connectivity back to users/partners. Treat this as your “clean room” landing zone when your primary cloud stumbles. - Refactor the critical path for region/provider agility
Abstract service discovery (DNS + app routing) and consider portable data patterns:
- Database replication or dual-writer patterns where appropriate
- Change-data-capture (CDC) pipelines to keep secondary stores warm
- Storage replication with immutability for integrity
- Rationalize identity
Ensure IdP and secrets management function independently of the impacted provider. Consider on-prem/privately hosted IdP failover so authentication is not a hostage to the outage. - Invest in observability that spans providers
Telemetry, tracing, and synthetic checks must work in primary and failover planes. Include external DNS monitoring and edge health in canarying. - Practice the playbook
Run tabletop and live failover exercises. Validate your mean time to redeploy (MTTRd) to the private cloud. Document rollback criteria and customer comms templates.
Why a Private Cloud Changes the Game
IT Vortex Private Cloud is architected to be your independent “Plan B”—a fully managed, VMware-powered environment with enterprise-grade SLAs, predictable latency, and migration tooling that preserves your existing VMware skillsets and runbooks. It’s a safety valve when the public cloud is impaired and a strategic hedge against correlated failures, compliance challenges, or abrupt cost shocks.
What that means in practice:
- Rapid workload mobility using VMware HCX-class replication and bulk migration patterns (zero-downtime options for select workloads)
- Network continuity with software-defined overlays and pre-peered connectivity to your premises, SaaS, and public cloud edges
- Immutable backups and DRaaS with testable failover/failback and compliance-grade retention
- Operational governance aligned to ISO/SOC standards and your sector’s regulatory posture
- Runbook codification: We document and rehearse the exact steps to swing traffic, elevate capacity, and validate data integrity—so you shift from hope to repeatable execution
When incidents like Oct 20 occur, we mitigate your blast radius by executing a structured failover to private cloud, keeping critical processes online, and giving your teams—and your customers—the time and stability to breathe.
Case-Study-Style Scenarios: Turning an Outage Into a Non-Event
- Fintech Transaction Core
- Before: Single-region AWS stack using DynamoDB + API Gateway; DNS hosted in Route 53
- After: Dual-write ledger feed to IT Vortex private-cloud relational store; Anycast DNS and secondary DNS authority; pre-approved firewall/egress to core banking partners
- Outcome: When US-EAST-1 stumbles, API traffic cuts over to private cloud; transactions queue locally; RPO < 60s, RTO < 15m; no regulatory breach events
- SaaS Collaboration Service
- Before: Serverless-heavy single provider; identity bound to cloud-native IdP
- After: IdP hot-hot in private cloud; session stores replicated; object storage mirrored with immutability
- Outcome: End-user login and content retrieval maintain >99.9% availability under public-cloud brownouts
- E-commerce & Fulfillment
- Before: Monolithic in US-EAST-1 for latency to East Coast; single dependency chain to managed data services
- After: Split-brain ready app tier; CDC pipelines to private-cloud inventory DB; WAF/edge policies primed
- Outcome: Catalog, cart, and checkout survive provider issues; warehouse ops continue; no lost weekend revenue
Board-Room Talking Points: From Outage to Operating Model
- Resilience is now a board metric. Track MTTRd (mean time to redeploy) to an independent plane—not just MTTR for a single provider.
- Concentration is a financial risk. Model downtime cost, customer churn, SLA penalties, and PR exposure against the cost of a private-cloud hedge.
- Compliance favors independence. In regulated sectors, auditors increasingly want to see a viable recovery environment not administratively bound to the impacted provider.
- Talent and runbooks matter. A plan you can’t practice is a plan you don’t have. Bake quarterly failovers into the operating cadence.
Key Takeaways
- AWS Outage October 20, 2025 exposed systemic single-cloud risk and US-EAST-1 regional dependency. (Reuters)
- Root cause involved DNS resolution to DynamoDB endpoints—cascading to load balancers and dependent services. (Amazon News)
- Affected services included Snapchat, Fortnite, Roblox, Alexa, Ring, Coinbase, Robinhood, and more, demonstrating cross-industry blast radius. (The Verge)
- Business continuity strategy must evolve to multi-region, multi-provider design with an independent private-cloud failover capability.
- IT Vortex Private Cloud delivers the alternate landing zone to fail over critical workloads during public-cloud incidents, protecting uptime, compliance, and brand trust.
Frequently Asked Questions
Q: We’re already multi-AZ on AWS—aren’t we safe?
A: Multi-AZ is essential but insufficient when control-plane, DNS, or managed data services in a single region fail. You need region escape hatches and, ideally, provider independence.
Q: How fast can we fail over to IT Vortex Private Cloud?
A: With pre-staged replication, network peering, and rehearsed runbooks, we routinely target RTOs measured in minutes and tight RPOs, subject to your application/data patterns.
Q: Isn’t multi-provider too complex or expensive?
A: Complexity without process is expensive. We productize the complexity—architecture blueprints, automation, and playbooks—so your cost per nine of availability is actually lower over time.
Q: What about data integrity and compliance?
A: We design with immutability, chain-of-custody, and auditable event trails end-to-end, aligned to ISO/SOC and industry-specific requirements.
Your Next Step: Make Outages Boring
Outages will happen. The question is whether they become existential dramas or boring footnotes in your weekly ops review. Yesterday’s AWS event was a wake-up call: “too big to fail” is just “too big a target.” The answer isn’t abandoning hyperscale—it’s de-risking it with independent recovery capacity and provider-agnostic design.
IT Vortex is the force multiplier that makes resilience repeatable:
- Assessment & Architecture: Dependency mapping, RPO/RTO design, region/provider escape routes
- Build & Migrate: Replication, HCX-assisted mobility, network interconnects, identity continuity
- Operate & Prove: Quarterly game-days, compliance artifacts, SLA reporting, continuous optimization
Ready to turn outages into non-events?
Let’s build your private-cloud failover strategy now—before the next headline.
Sources & Further Reading
- AWS post-incident communication and timeline (DNS to DynamoDB endpoints; mitigation windows). (Amazon News)
- Reuters overview and impact across industries; user impact scale; regional concentration context. (Reuters)
- The Verge incident roll-up: services impacted; timing; DNS and EC2 internal network factors. (The Verge)
- ThousandEyes independent analysis on US-EAST-1 and dependent services. (ThousandEyes)
- The Guardian macro-risk framing: concentration of internet services in few providers; regulatory implications. (The Guardian)
Appendix: Companies and Services Reported as Impacted (Representative, not exhaustive)
- Consumer/Comms: Snapchat, Reddit, Signal
- Gaming/Media: Fortnite, Epic Games Store, Roblox, Prime Video, Pokémon Go
- Smart Home/Voice: Alexa, Ring
- Fintech/Crypto: Coinbase, Robinhood, Venmo
- SaaS/Collab: Airtable, Zapier, Canva, Slack (via dependencies)
- Public Sector/Education: HMRC (UK), university platforms (Canvas/Zoom access)
- Commerce: Amazon.com (select services)
Citations: (The Verge)
About IT Vortex
IT Vortex is a VMware-powered private cloud and managed services provider that operationalizes resilience at scale. We help enterprises and mid-market leaders de-risk single-cloud exposure with portable architectures, orchestrated failover, and governed runbooks that keep business outcomes on track—no matter what the internet throws at you.






















